Types of Cloud Computing Models
Overview
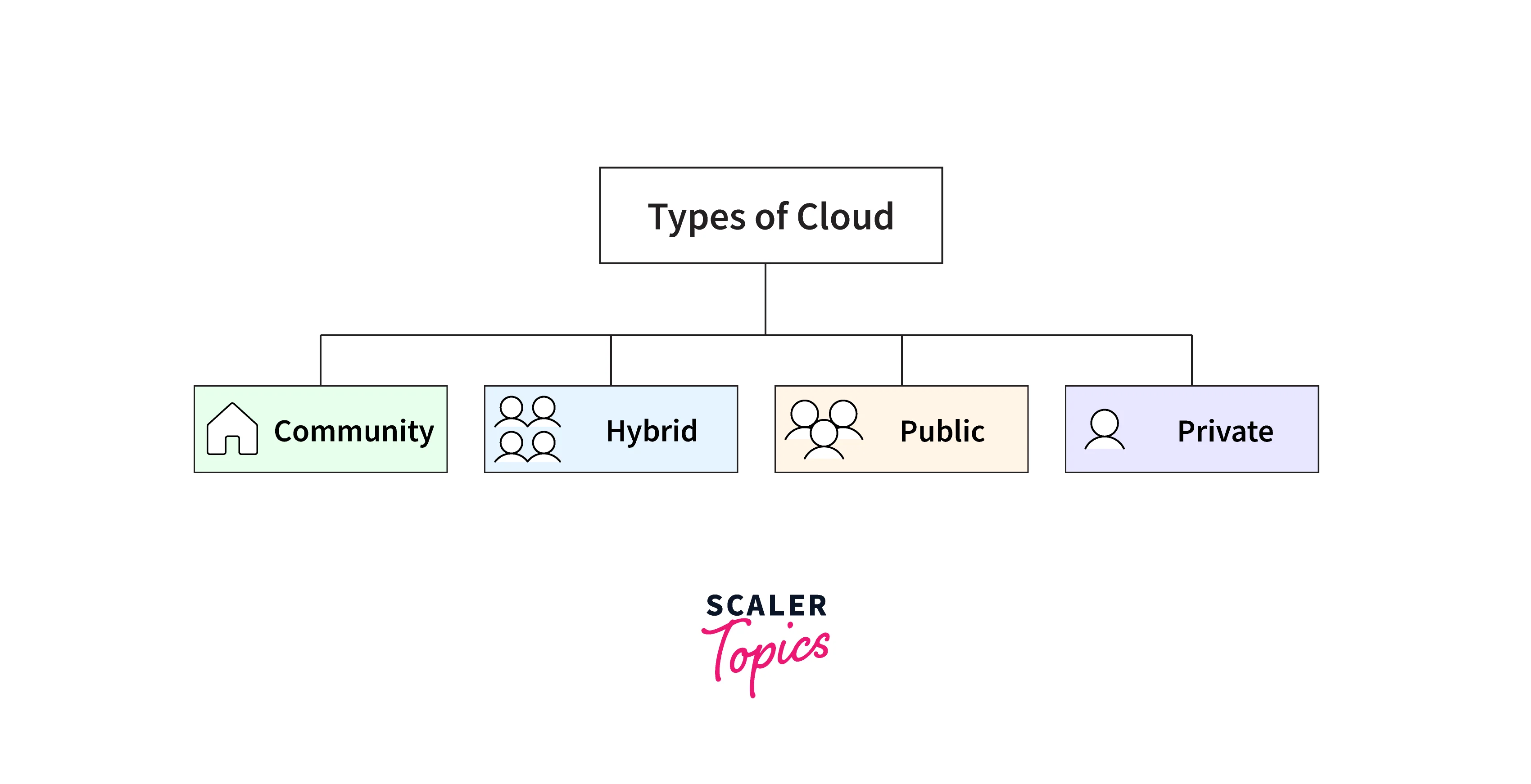
Cloud computing is the latest emerging concept in which we provide the distribution of computing resources as a service. Different types of clouds are available to us, such as public, private, hybrid, etc. There are different cloud computing models like IaaS, PaaS, SaaS, etc.
Types of Cloud Computing
Four different types of cloud deployment models exist. These deployment models vary depending on how they are implemented, how they are hosted, and who has access to them. Although all cloud deployment options are based on the same virtualization idea (the separation of resources from bare metal infrastructure), they vary in terms of location, storage capacity, accessibility, and other factors. One should evaluate the various levels of security that Public, Private, Hybrid, and Community Clouds offer and the level of management necessary depending on the type of data you are working with.
Public Cloud
Public clouds are run by third parties (Cloud Service Providers, CSP in short) who offer cloud services to the general public over the internet with pay-as-you-go invoicing options. They provide ways to reduce the cost of IT infrastructure and develop it into a viable choice for managing peak demands on local infrastructure. Small firms can launch their operations without making significant initial investments by depending solely on public infrastructure for their IT requirements, making public clouds the go-to choice for these companies. Multitenancy is one of the essential properties of public clouds. A public cloud is designed to service many users, not just one particular client. A user needs a virtual computing environment that is distinct from other users and most likely isolated. Examples include Microsoft, Google App Engine, IBM SmartCloud Enterprise, Amazon elastic compute cloud (EC2), and Windows Azure Services Platform.
Private Cloud
Private clouds are distributed systems that operate on private infrastructure and give users access to computer resources that are dynamically allocated. Private cloud users/organizations receive exclusive infrastructure that is not shared with any other users/organizations. There may be additional plans that regulate cloud usage and proportionally charge the various departments or areas of an organization in place of the pay-as-you-go model used in private clouds. When using a private network, the security and control levels are at their maximum. The costs are borne entirely by one person or organization; they are not distributed among any other people or organizations. The user is responsible for managing the Private Cloud, and the CSP does not offer any cloud management services. HP Data Centers, Ubuntu, Elastic-Private cloud, Microsoft, and other companies offer private clouds.
Private clouds are used to do specific tasks, including reliable clustering, data replication, system monitoring and maintenance, disaster recovery, and other uptime services. When deploying and running applications in accordance with third-party compliance standards, specific procedures must be in place. Given the public cloud, this is not feasible, but on the other side, it is completely possible to implement an SLA in the case of a private cloud. There are also a few limitations in using private clouds on a large scale. The private cloud is reachable only in a specific location. The accessible range is thus minimal. Since client data and other sensitive information do not transfer outside the private infrastructure, security issues in the private cloud are reduced. Consequently, managing and running cloud services requires competent personnel.
Hybrid Cloud
A hybrid cloud is created by merging the resources of the public cloud and the private cloud. For the same reasons, it is also known as heterogeneous clouds. The inability of private deployments to scale on demand and effectively handle peak loads is a significant disadvantage. Thus public clouds are required in such cases. As a result, a hybrid cloud utilizes the functionality of both public and private clouds. Because it is created through a distributed system, it is less expensive than other clouds. It minimizes the latency of the data transfer process while being effectively quick and inexpensive. The most crucial factor is security. Because it uses a distributed system network, hybrid clouds are completely safe and secure.
Community Cloud
Community clouds are distributed systems built by combining the capabilities of many clouds to cater to the unique requirements of a particular industry, community, or business sector. However, it is challenging for companies to split up their responsibilities. Companies that share concerns or tasks in a community cloud pool their infrastructure resources. A company or a third party may control the cloud.
Community cloud is economical because many different businesses/communities share the same cloud. Organizations that desire a collaborative cloud with greater security features than the public cloud should use a community cloud. Security-wise, it surpasses that of the public cloud. It offers a setting that is cooperative and distributive. Thanks to community clouds, we may share cloud resources, infrastructure, and other capabilities between different enterprises.
There are a few limitations to using community clouds as well. Not all businesses should choose community cloud. The private cloud has better security features as compared to hybrid clouds. Additionally, using hybrid clouds could be difficult when there is a lack of teamwork. All community members share a limited amount of data storage and bandwidth.
Multi-cloud
Multi-cloud is a cloud deployment model in which a company distributes applications and services across a number of different clouds. Two or more public clouds, two or more private clouds, or a combination of public, private, and edge clouds may make up these clouds.
Using a variety of cloud platforms and services, businesses are accelerating the next stage of their digital transformation by accelerating the creation of new apps and app transformation. Since multi-clouds best serve their business goals and application requirements, companies are choosing to deploy apps on public, private, and edge clouds. The use of multi-clouds ensures enterprise sovereignty and prevents vendor lock-in. Concerns about total cloud spending, data sovereignty, vendor dependence, and lock-in are growing. As a result, businesses will keep dispersing their estate throughout various surroundings.
Applications need to be deployed to the edge, closer to physical objects and users, to achieve the next generation of improvements in automation, efficiency, and improved consumer experiences in the logistics, retail, and manufacturing sectors. Multi-clouds encourage the growth of the distributed workforce because it is the new reality for businesses. The emerging hybrid workforce problem is to secure, manage, and enable workers and their devices to be productive wherever.
A Comparative Analysis of Different Types of Cloud Computing
Refer to the below table to study the important features of each of the models and see an outline of what each one can achieve for you:
| Feature compared | Public Cloud | Private Cloud | Community Cloud | Hybrid Cloud |
|---|---|---|---|---|
| Security and Privacy | Low | High | Comparatively Higher | High |
| Reliability | Low | High | Comparatively Higher | High |
| Control over the data | Very Less | High | High | High |
| Ease of setup and use | Easy | Requires Prerequisite Knowledge | Requires Prerequisite Knowledge | Requires Prerequisite Knowledge |
| Cost | Cheapest | Most expensive | Cost is shared among members of the community | Between private and public clouds |
Making the Right Choice for Any Type of Cloud Computing According to Business Requirements
Making sure you choose the correct cloud providers has become essential to long-term success as more and more IT systems are being externalized. However, there is a sizable market, and numerous companies offer a wide range of services, ranging from industry behemoths like Microsoft, Amazon, and Google to smaller niche firms providing customized services. So how does one pick the best cloud service out of them? The solution is a clearly defined selection and procurement process that is appropriately weighed toward your particular set of needs. The requirements and evaluation standards you employ when choosing a cloud provider will be particular to your business. However, any service provider evaluation will often concentrate on a few key criteria. Let us see the essential factors to consider while making the right choice for any type of cloud computing as per the business requirements.
Certifications
The adherence to industry best practices and standards is demonstrated by providers who follow recognized standards and quality frameworks. Standards can be quite helpful in narrowing down the pool of potential suppliers, even though they might not ultimately influence which service provider you select. For instance, if security is a top concern, search for providers who have received accreditation from the government's Cyber Essentials Scheme or ISO 27001. Numerous standards and certifications are being offered these days. In general, keep an eye out for structured processes, efficient data administration, effective knowledge management, and visibility of the status of your services. Additionally, be aware of the provider's plans for providing resources and assisting with ongoing adherence to these standards.
Privacy and Security
Perhaps a policy might already be in place for classifying the data based on its sensitivity or the location where it is stored. It should be ensured that data traveling to or within the cloud must be encrypted to safeguard it while it is in transit. Additionally, sensitive volumes should be encrypted at rest to reduce exposure to unauthorized administrator access. Sensitive data should be encrypted in object storage, typically using file/folder or client/agent encryption. It is good to check that the cloud provider's data loss and breach notification procedures are in line with your organization's risk tolerance and any applicable legal or regulatory requirements by learning about them.
The organization should be familiar with personal data's legal or data privacy requirements. The location where the data is stored and the consequent local legislation to which it is subject may play a significant role in the decision-making process. If users have particular needs and obligations, they should search for service providers who provide a choice and control over the country where the data is kept, handled, and controlled. Although cloud service providers should be open and honest about where their data centers are located, it is also the user's job to do their research.
Proper RoadMap/ Strategy
Verifying that the provider's platform and preferred technologies support your cloud goals and are compatible with your present environment is important. The organization should check whether the provider's cloud architectures, standards, and services work for the respective workloads and management preferences. Estimate the amount of re-coding or customization necessary to make the business workloads compatible with their platforms. Numerous service providers provide comprehensive relocation services and even aid in the planning and assessment stages. Make sure you have a solid grasp of the support provided, connect it to the project's tasks, and select who will handle what. Service providers frequently have technical personnel on staff who can close gaps in your migration teams' skill sets.
One should also inquire about the service provider's future development plans. How do they want to stay innovative and expand over time? Does their long-term plan meet your business needs? Commitments to particular technologies or suppliers and how interoperability is facilitated are crucial issues to consider. Can they demonstrate deployments that are comparable to the ones you are planning? A feature, service, and integration plan is highly desirable, especially for SaaS providers. Under your specific cloud plan, you might also wish to consider the services providers can provide. This is less critical if you intend to employ different best-of-breed services from various providers. Still, if you prefer to use just a few major cloud service providers, they must provide a decent selection of complementary services.
Service Level Agreements (SLA) and Contracts
The lack of industry standards for building and describing cloud agreements contributes to their perceived complexity. Many jargon-happy cloud companies use needlessly complex words to mislead their clients when discussing SLAs purposely. The most recent version of the ISO standards for service level agreements, ISO/IEC 19086-1:2016, addresses this to some extent and provides a useful framework for evaluating provider agreements. Contracts may range from pre-written terms and conditions that are agreed upon online to individually drafted contracts and SLAs. It all depends on how big the Cloud Service Provider is compared to its clients. Smaller CSPs are more inclined to engage in discussions, but they may also be more inclined to accept bespoke terms that they may be unable to support. Always ask companies willing to offer flexible terms how they intend to support this variation, who will be responsible for it, and what procedures will be employed to regulate it. SLAs should have three main parts: service level goals, policies for remediation, fines/incentives about these goals, and exclusions and restrictions. Accessibility, service availability (often uptime as a percentage), service capacity (what is the maximum number of users, connections, resources, etc.), response time, and flexibility are among the specific service level goals (SLOs) covered in an SLA.
Performance and Reliability
There are several ways to evaluate a cloud service provider's reliability. Start by contrasting the service provider's SLA performance over the previous one to two years. Although some service providers make this information readily available, others should as well if asked. The client should also not expect the cloud services to operate all the time flawlessly; thus, expecting zero downtime is unrealistic. What counts is the cloud provider's response to an expected/unexpected outage. Ensure the monitoring and reporting tools you can access are sufficient and work with your overall management and reporting systems.
Ensure that the chosen service provider has developed, documented, and tested procedures for handling scheduled and unscheduled downtime. They should have policies and plans detailing how they intend to get in touch with customers during times of disruption, including prioritizing issues, communicating on time, and gauging their seriousness. When service faults occur, be aware of the remedies and liability restrictions provided by the cloud provider.
The client can also examine the provider's disaster recovery policies, procedures, and capacity to meet their expectations for data preservation. This should cover the data's importance, the sources of the data, scheduling, backup and restoration procedures, integrity checks, etc. In the service agreement, roles and responsibilities, escalation procedures, and who bears the burden of evidence must all be precisely outlined. This is crucial because your team may often be in charge of carrying out some of these procedures. If the provider's umbrella terms and conditions do not cover the costs related to recovery, think about getting supplementary risk insurance.
Exit Planning/Migration Support
When a customer finds it challenging to convert to a competitive cloud provider after using the current provider's service, this situation is described as vendor lock-in. Vendor lock-in is frequently caused by proprietary technologies that are incompatible with those of competitors. It may result from a variety of factors, such as flawed procedures or contractual restrictions. Cloud services that largely rely on specialized or distinctive proprietary components may impact your portability to other providers or internal operations. This is particularly true if programs must be redesigned to run on a platform provided by a service provider. Make sure your supplier of choice uses the least amount of proprietary technology or that you employ the fewest services that restrict your freedom to switch providers or migrate away to reduce the danger of vendor lock-in.
To reduce the risk of lock-in, it is ideal to choose value-added services with equally effective and affordable alternatives. Finally, you should weigh the undeniable advantages of using the services provided by one specific cloud provider against the dangers of becoming overly dependent on that particular provider. Ensure that you have a defined exit strategy in place before you start dating. Learning about a CSP's procedures before signing a contract is important because switching from their service isn't always simple or quick. Take into account your access options as well as the status and duration of the provider's storage of your data.
Conclusion
- Although all cloud deployment options are based on the same virtualization idea (the separation of resources from bare metal infrastructure), they vary in terms of location, storage capacity, accessibility, and other factors.
- There are different types of clouds, namely public clouds, private clouds, hybrid clouds, community clouds, and multi-clouds.
- Comparative Analysis of different types of cloud computing
- Making sure you choose the correct cloud providers has become essential to long-term success as more and more IT systems are being externalized.
- Verifying that the provider's platform and preferred technologies support your cloud goals and are compatible with your present environment is important.
