AWS Systems Manager Parameter Store
Overview
Amazon System Manager is one of the free services provided by AWS. It has a whole lot of capabilities to monitor and troubleshoot an individual instance and a fleet of instances. AWS SSM Parameter Store is one of the components among the several features available in AWS System Manager or AWS SSM. In 2017, the AWS SSM Parameter Store was introduced. The AWS SSM Parameter Store is used to store and retrieve data and secrets that will be used in the application later using the AWS SDK.
Introduction to AWS Systems Manager Parameter Store
Before starting with the AWS SSM parameter store, we should know what a parameter is.
The parameter is the piece of information or data that can be passed through the application deployed in any one of the AWS Services, Customers can store the parameter as an individual entity and integrate it with their application.
- The AWS SSM parameter store helps customers to store the parameter in the AWS region of their choice.
- In simple terms, an AWS SSM Parameter Store will store the customer’s credentials and other important things like product keys in a single place within a region.
- By doing this, we can easily secure our data or credentials for automation and custom scripts.
- In those scripts, let's say we want to update them. Customers may have hundreds of scripts with administrator credentials in them. Instead of manually going and changing the value in that script. Customers can refer to those values in an SSM parameter store.
- We can easily and quickly update the value of all parameters in a single place called an SSM parameter store.
One of the other aspects of using an SSM parameter store is that customers can choose to save those parameters securely; they can opt for a secure string option to encrypt and store their parameters. It also helps them with an extra layer of security using the AWS KMS (Key Management Service) and satisfies all the standard compliance requirements.
Who Should Use AWS Parameter Store?
AWS recommends using the AWS parameter store for the below users and customers.
Customers
If any AWS customers would like to configure data in a centralized location for their application, they should utilize the AWS SSM parameter store. AWS SSM Parameter store is generally available to all AWS customers.
Developers
Developers who are managing multiple credentials and require frequent data changes in their applications should use the AWS SSM Parameter Store.
System Administrators
AWS System Administrators or Owners of AWS Accounts who want to get notified when their secrets or passwords are changed should consider using the AWS SSM Parameter Store.
Features of AWS Parameter Store
Data Validation
- We can create a new SSM parameter and then validate it with the AWS compute resources, such as the EC2 instance.
For example,
- We can declare the AMI as parameter aws:ec2::image as the data type. then the SSM parameter will be validated asynchronously.
- The user or application sending a request should have the necessary permissions for the EC2 resource and SSM parameters as well.
Organize Parameters
-
Customers can tag their parameters and identify them. It will help them segregate the mission-critical parameters into less critical parameters.
-
It will also assist them in separating the parameters by project, environment, domain, and department.
Reference Secrets
- Secret Manager and the AWS SSM Parameter Store are natively integrated. So customers can refer to the secrets in the secret manager in the AWS SSM parameter store.
Note: These referenced secret features will only apply to selected AWS support services.
Label Versions
- Using Alias, we can create a label for our parameter. It will help the customers understand the purpose of the parameter.
- Whenever the parameter is updated or any change happens to the parameter, It will get versioned. Customers will thus have access to all versions of the parameter, from those created to those deleted.
Accessible from other AWS Services
-
Data stored in the parameter can be retrieved or referenced by other AWS services. The main purpose is to make it easy to configure data, state management of resources, automation, and CI/CD deployment.
-
According to the AWS Blog, the below-mentioned services are the most commonly used AWS services that utilize the AWS SSM Parameter Store.
-
Amazon Elastic Compute Cloud (Amazon EC2)
-
Amazon Elastic Container Service (Amazon ECS)
-
AWS Secrets Manager
-
AWS Lambda
-
AWS CloudFormation
-
AWS CodeBuild
-
AWS CodePipeline
-
AWS CodeDeploy
-
Native AWS Service Integration
- There are certain AWS services that are natively integrated with the AWS SSM Parameter Store for secure communication and monitoring purposes. They are
- AWS SNS
- Amazon Eventbridge
- AWS Cloudwatch
- Customers create an event bridge rule with an action for any changes in the parameter store service.
- After selecting the service and action, they can choose the SNS topic to receive a notification.
- By doing this, customers will get notified if someone mistakenly changed the parameter by using the AWS console or CLI.
Encryption Using AWS KMS
- AWS KMS is a key management service. AWS provides an AWS KMS key to encrypt the data stored in the parameter store. Customers can also provide their customer-managed key (CMK) to encrypt their data.
Note: The secure string data type only supports AWS KMS.
What is a Parameter?
The parameter is a piece of information or data that can be used for the next set of actions for the application.
Example Scenario
Day - November 2022 In the next two months, the date will be January 2023. Consider an insurance company that updates all its websites with the current year's date every year.
They can achieve it in two ways.
- Change the date and year in the application code manually and deploy it.
- In the application code, use the environment variable and refer to the environment variable in the AWS SSM Parameter Store.
- By choosing the second option, customers don’t need to deploy the entire code again; the value will be dynamically updated.
- We can simply update the parameter in the AWS SSM Parameter Console. The service will pick up the latest value by default.
- In some cases, cache invalidation may be required if any cache service is incorporated into their architecture.
How to Use AWS Parameter Store?
Requirement:
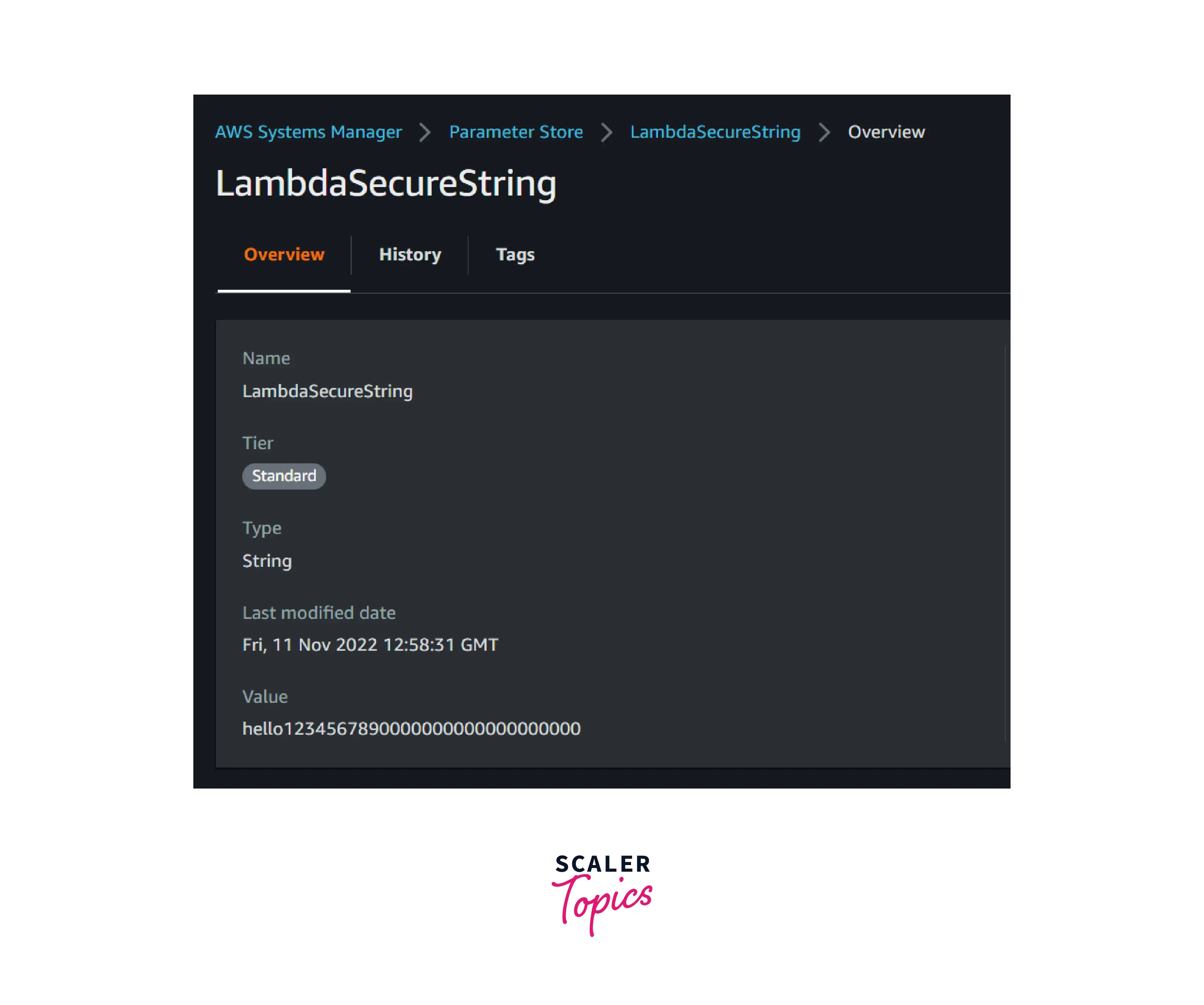
- SSM parameter named LambdaSecureString
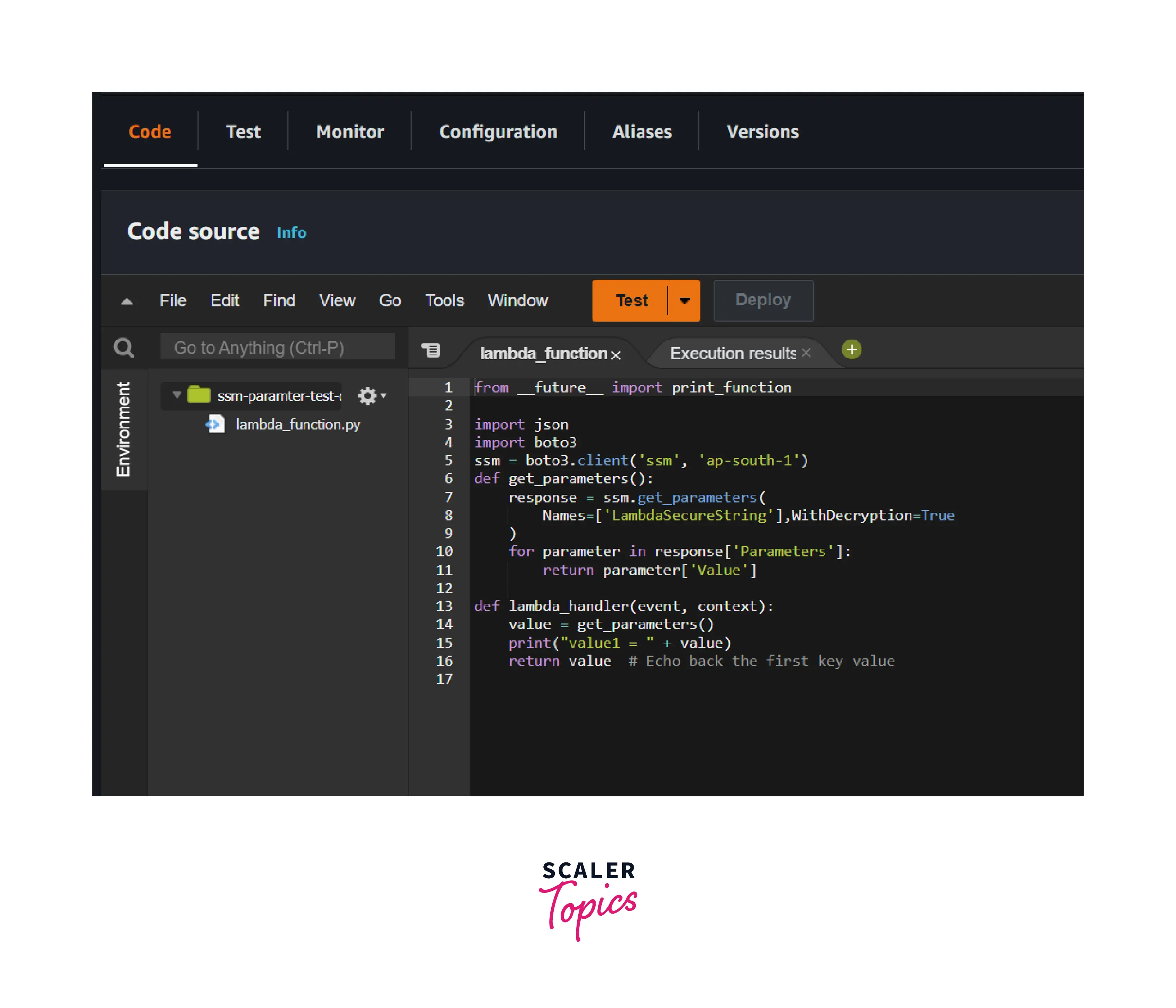
- Lambda function with SSM permission attached
The image below depicts the LambdaSecureString parameter available in the AWS account.
As per the below Python code, it will retrieve the value of a parameter stored in the AWS SSM parameter.
The output image below shows that the lambda code sends an API call to the parameter and returns the value of the parameter.
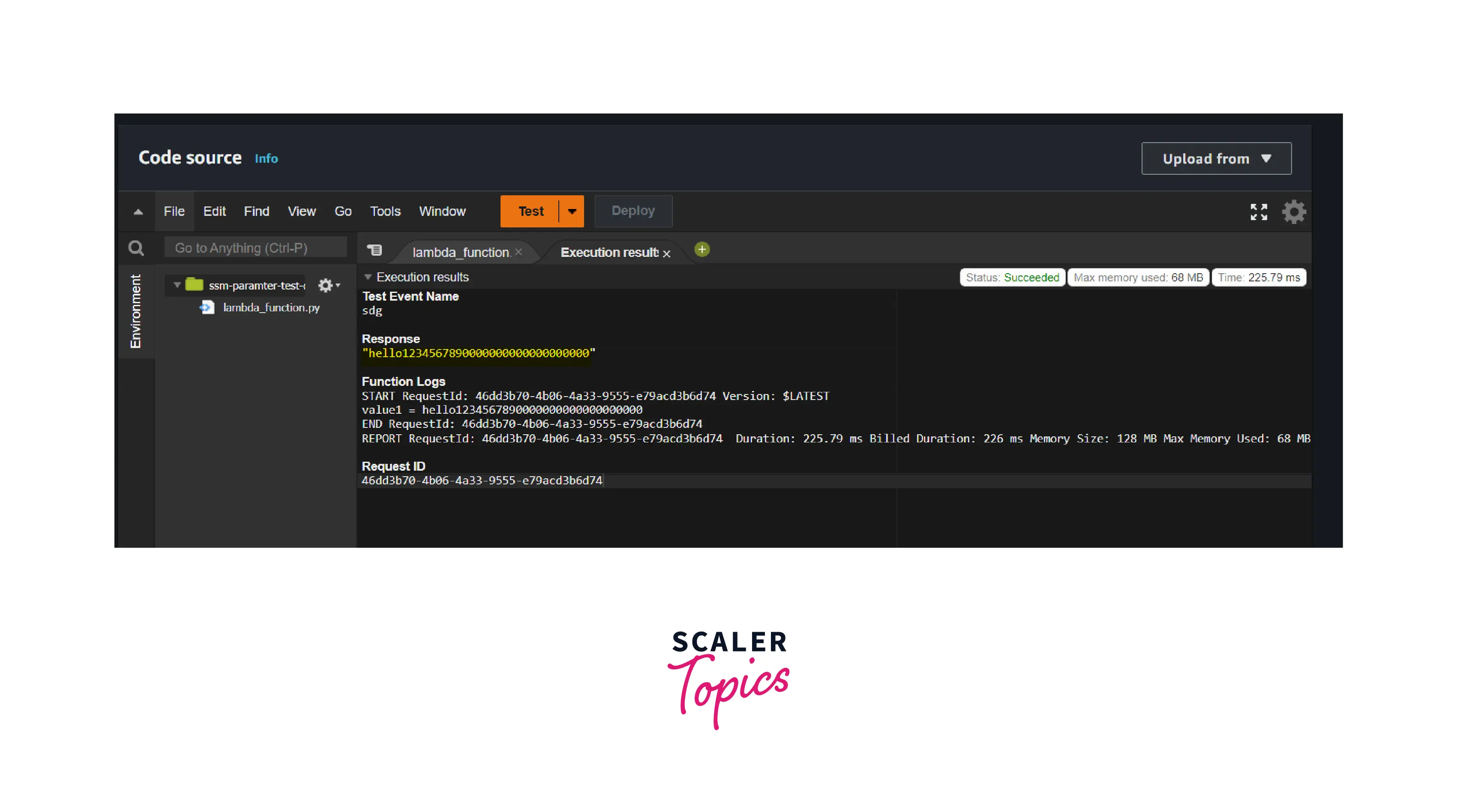
Similarly, customers can refer to the parameters in their application code depending on their AWS SDK.
AWS Parameter Store Use Cases
Centralized Data Configuration
Customers can store secrets, credentials, and application-critical data in a central location and refer to it.
Highly Available
Customers should consider using AWS SSM parameters if the application is data-intensive. We can route the read request to the AWS SSM instead of the application-deployed server.
Serverless CI/CD and Data Pipeline
For DevOps and data pipelines, the dynamic configuration of data is unavoidable. Customers consider using the SSM parameter store in this kind of scenario for versioning purposes.
Working with AWS Parameter Store.
In this topic, we are going to create, modify and delete the parameter in the AWS SSM parameter store via Console and CLI.
Before doing the demo, there are certain procedures we need to keep in mind and follow while creating the parameter. They are
| No | Components | Constraints |
|---|---|---|
| 1 | Case Sensitive | All the SSM parameters are case sensitive |
| 2 | Size Limit | 1100 characters per parameter name |
| 3 | Spaces | Spaces are not allowed in the parameter name |
| 4 | Allowed character Prefix | prefixes such as /somename and /somname/secondname are allowed |
| 5 | Valid AMI format | aws:ec2 |
| 6 | Hierarchy Level | Maximum of 15 levels of hierarchical depth are allowed |
Parameters are unique in the region. meaning you can create the same parameter name in different regions but not in the same region.
Note: The IAM user should have SSM parameter store read and write permission to do the below demo.
Create a Parameter via the Console
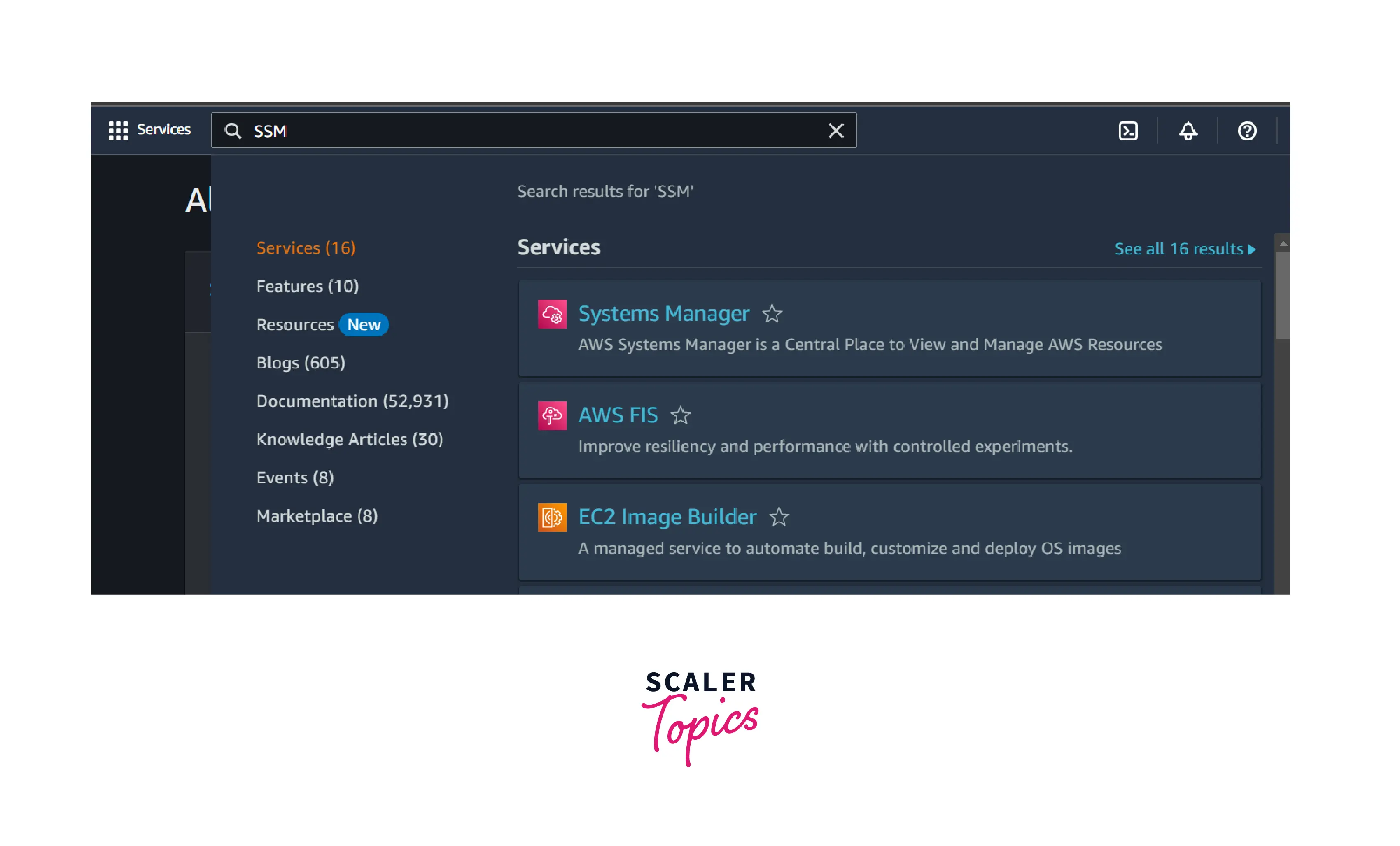
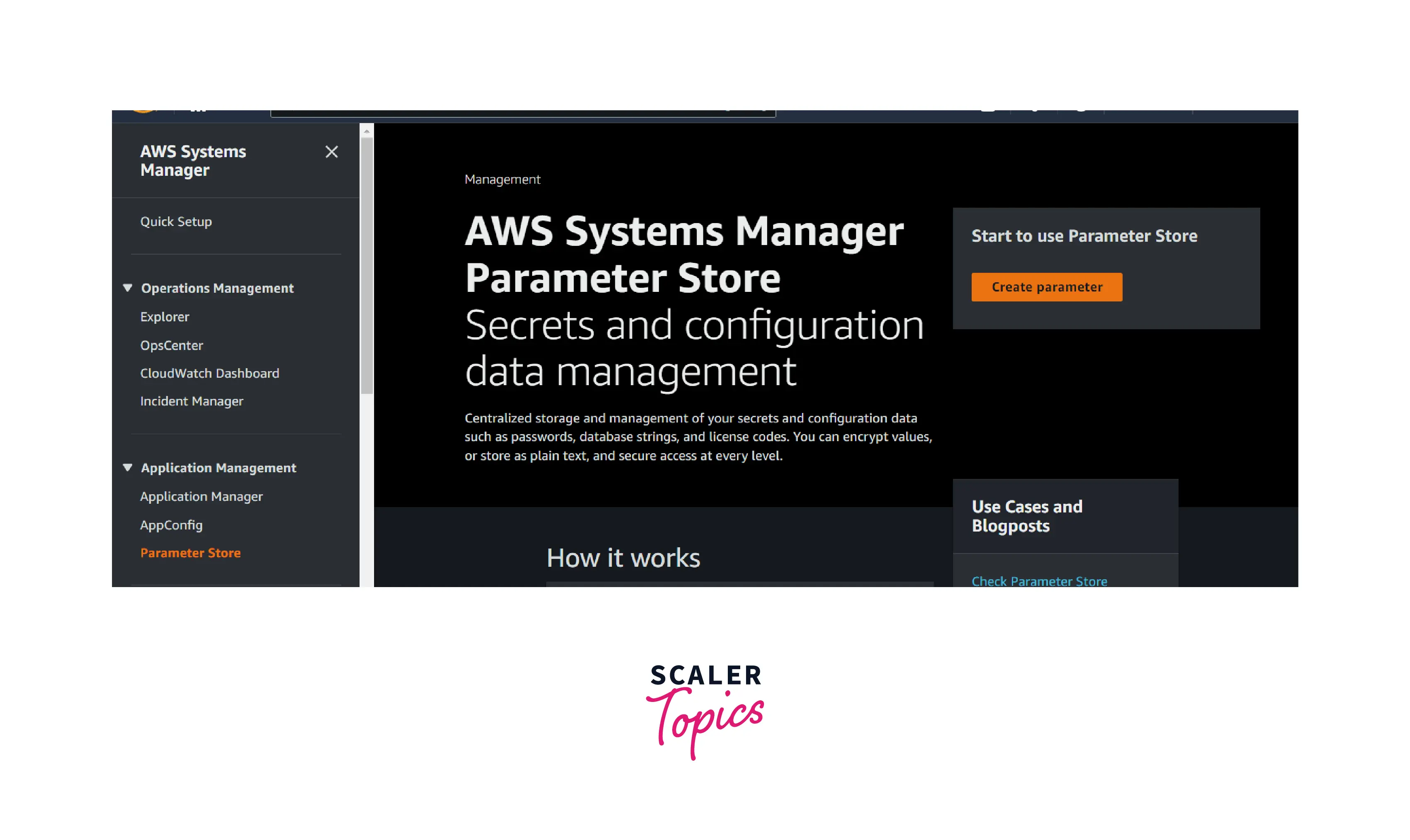
Logged in to the AWS account and enter SSM in the search bar and select it.
In the SSM home page, select the parameter store option which is placed in the left navigation pane under the App Management
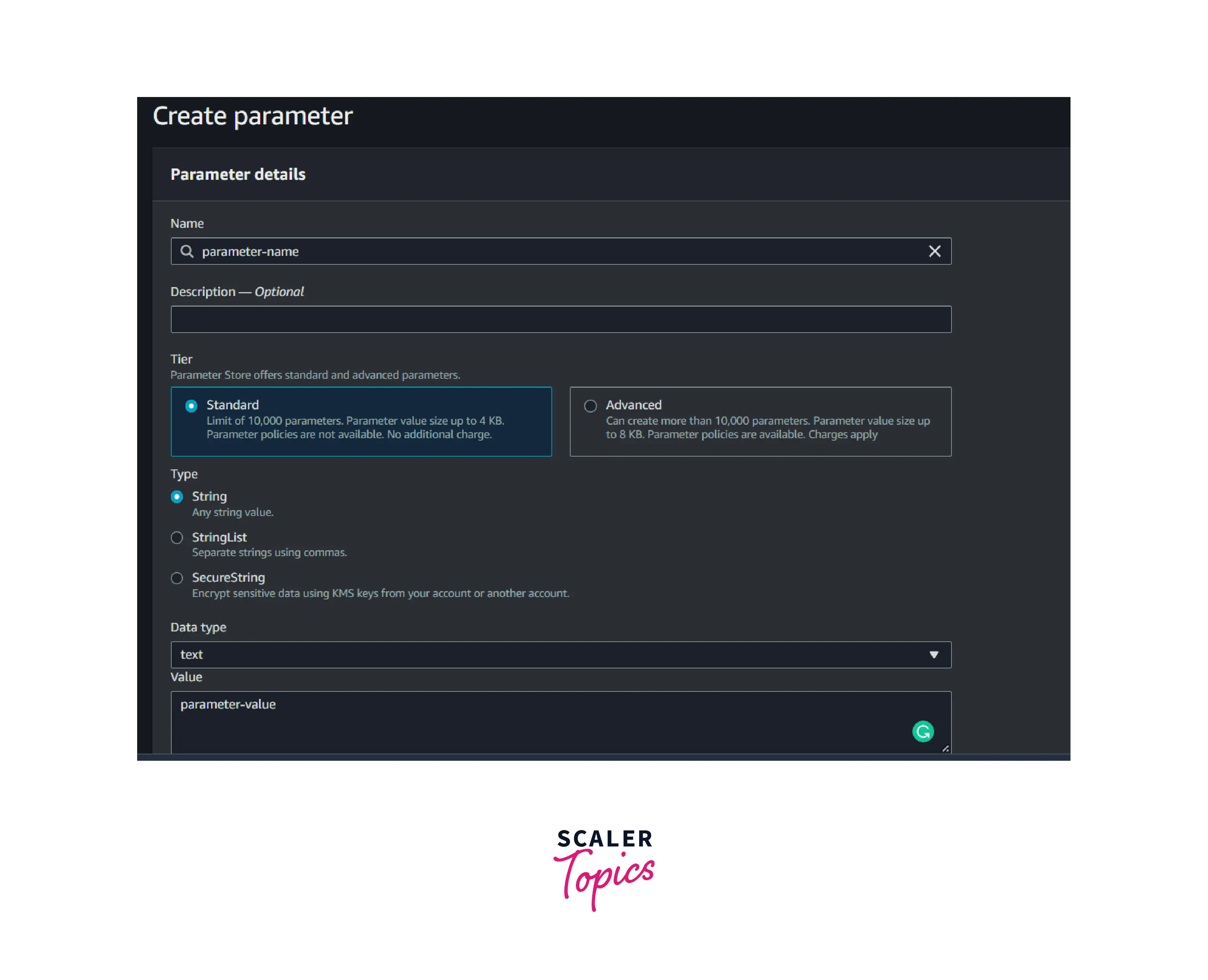
Select Create Parameter
-
Enter the below name or any unique name of your choice
- Name: parameter-name
- Type: string
- Value: parameter-value
Create a Parameter via CLI
Linux or macOS
Windows
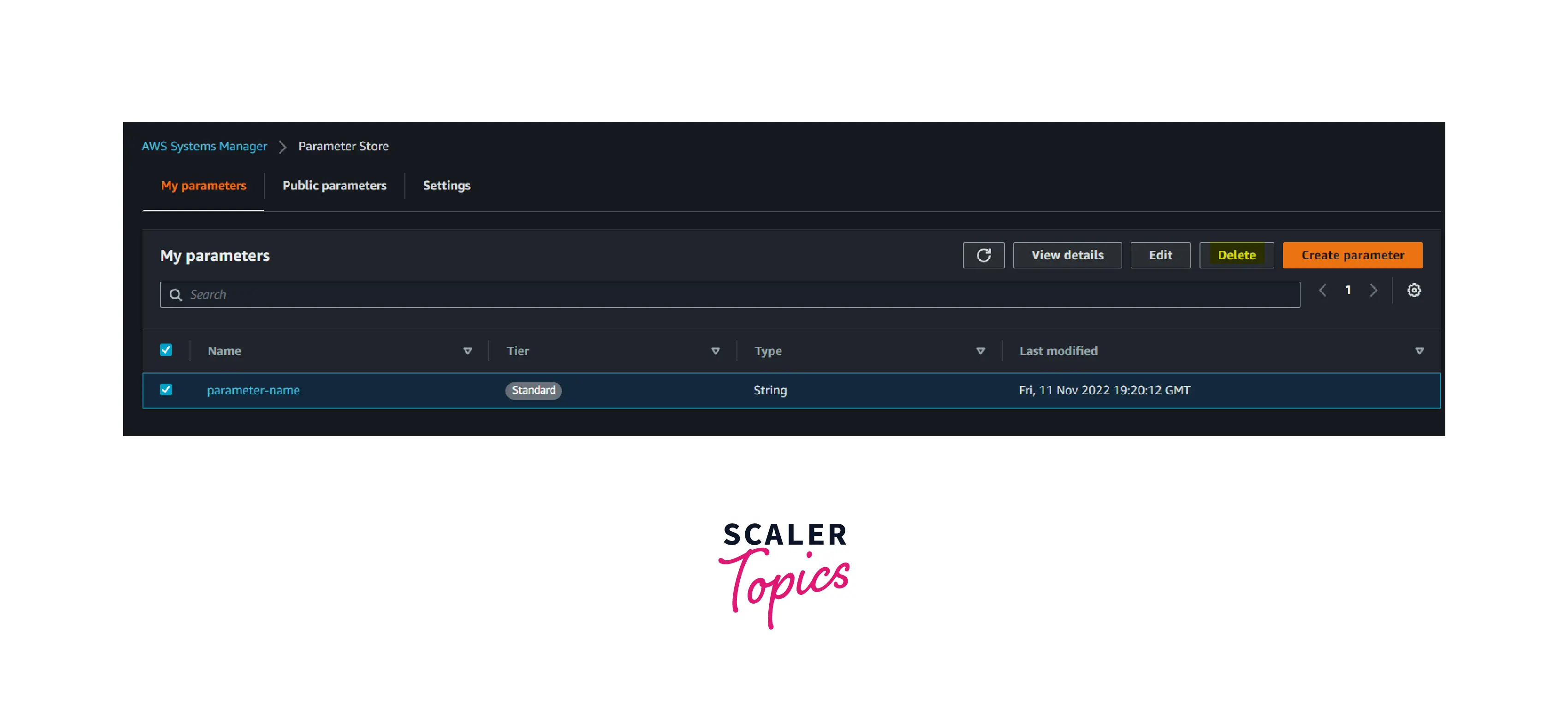
Delete a Parameter via the Console
-
Go to the AWS SSM dashboard and select the parameter store.
-
Select the parameter you wish to delete and click the delete button to delete the selected parameter.
Delete a Parameter via CLI
Linux/Windows/macOS
Kindly refer to the below documentation for more details about the AWS SSM parameter.
Reference: Working with Parameter Store - AWS Systems Manager
Benefits of AWS Parameter Store
- The AWS SSM parameter helps customers configure data management in a single, central location.
- AWS SSM is a highly available service. So customers don’t have to worry about retrieving a parameter from multiple services simultaneously.
- AWS SSM works with AWS KMS to encrypt the data stored in the parameter. This will provide an additional layer of security. Customers can choose their account KMS key or another AWS account KMS key.
- Serverless services such as Fargate and Lambda work seamlessly with AWS SSM parameters.
- Customers can also use the AWS SSM parameter in their application. i.e., cloud-agnostic. But they should configure the proper SDK and role credentials in their application code.
- AWS SSM Parameter also provides versioning and history of the parameter lifecycle.
- Using advanced options in the AWS SSM parameter, customers can set the expiry policy for the parameter.
How to Store Secrets Using AWS Parameter Store?
Consider the below Scenario:
An application deployed in the EC2 instances is requesting data from the RDS instance or DB instance. To access the RDS instance or DB instance, the application should pass the secrets, such as the DB username and password, via authentication. How to store the secrets using AWS the SSM parameter store?
- Customers can embed their secrets in their application code, which will be running in the EC2 instance.
Or
- They can use the AWS SSM Parameter Store. Here, they use the SecureString type to store the DB secret and then refer to that parameter in their code.
- By doing this, the application will fetch the secrets from AWS SSM and pass them to the DB or RDS.
- In the event of an EC2 instance or application code compromise, the secrets will not be affected.
Not only EC2, but customers can also store secrets and refer them to ECS, EKS, lambdas, codeDeploy, etc.
Create a Secret Parameter
Go to the parameter store and select create parameter.
Name: database-password
Type: SecureString
Value: thisismydbpassword
Click the Create button.
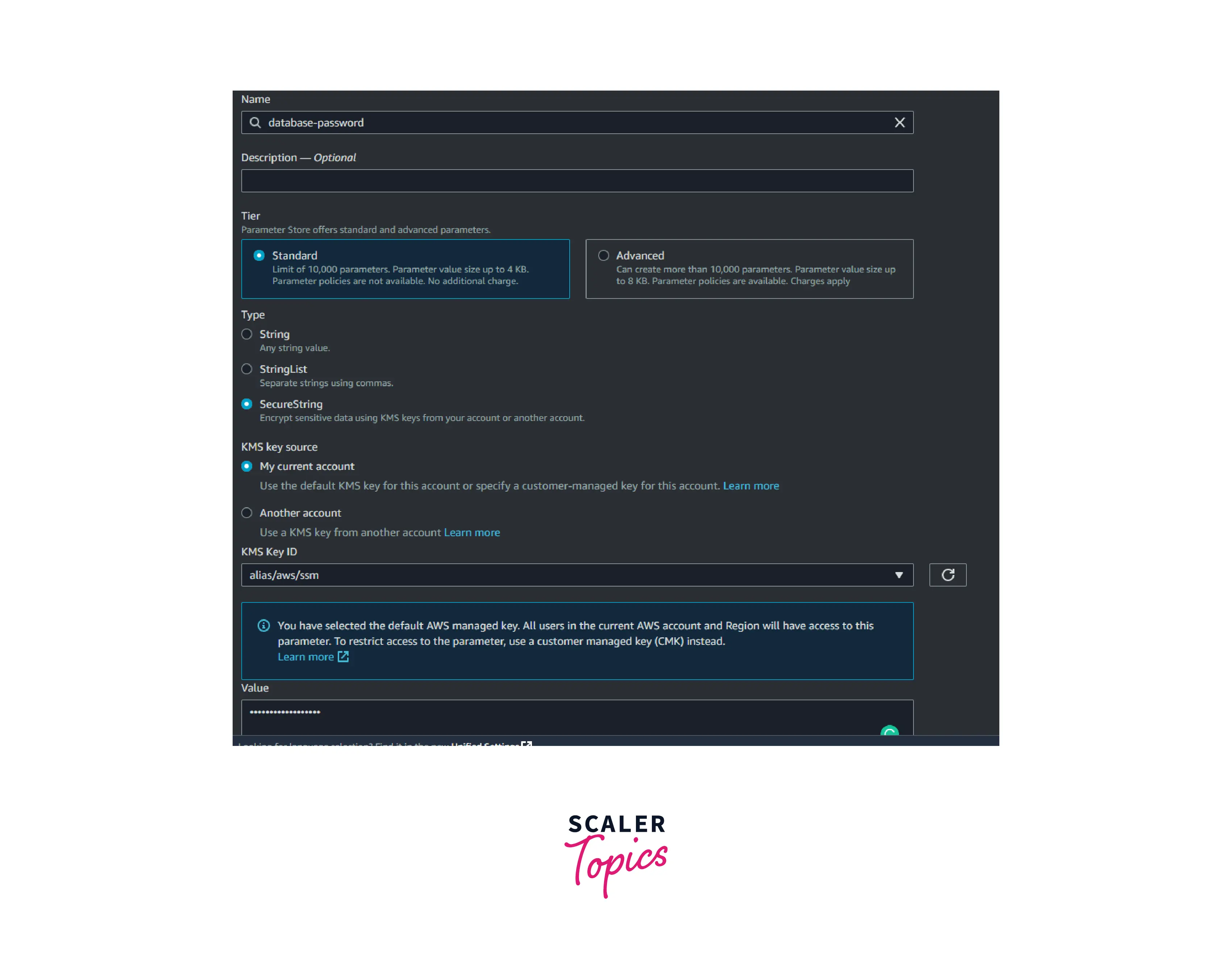
As you can see in the above image, the value is encrypted using the AWS KMS key.
Similarities and Differences between AWS Secrets Manager vs AWS Systems Parameter Store
| Parameter Store | Secrets Manager |
|---|---|
| It stores parameters as well as secrets | It stores secrets only |
| The value can independent of AWS resources | The secrets should be dependent on the AWS resources |
| Encryption enabled by SecureString Type. | Encryption enabled by default |
| It helps for configuring data in an application | It helps for storing and retrieving secrets only |
Pricing of AWS SSM Parameter Store
The pricing of AWS parameters depends on two things. They are storing the parameters, tier, and API calls made to the parameter.
| Tier | Standard | Advanced |
|---|---|---|
| Storage per month | $0.0 | $0.05 per advanced parameter per month |
| API Call per month | $0.05 per month per 10000 API calls | $0.05 per month per 10000 API calls |
Conclusion
- The AWS parameter store is a regional service used for configuring secret management, credentials management, and validation.
- It is highly available, so customers can achieve workflow management and automation without worrying about managing the data.
- It is easily integrated with AWS serverless services such as Lambda and API Gateway and compute services such as EC2, ECS, and EKS.
- The cost of storing and retrieving parameters is low when compared to AWS Secrets Manager.
- Customers can use the AWS Parameter Store to achieve abstraction and obfuscation of application data. It will increase the security posture of the customer’s application.
- By Using IAM policies, we can provide granular access control and permissions at an SSM parameter or API level.
- SSM Parameter with SecureString datatype values is encrypted using the customer’s AWS Key Management Service (KMS) customer master key (CMK) or the default KMS service key for their AWS account.
