EC2 Security Groups
Overview
Security is one of the shared responsibilities between you and AWS. **Security group** in AWS is the direct logical network component associated with the EC2 instance that helps us to operate on the **security of an EC2 instance** in a network.
What are Security Groups in AWS ?
-
In AWS, the Security group comprises a list of rules which are responsible for controlling the incoming and outgoing traffic to your compute resources such as EC2, RDS, lambda, etc.
-
Security groups in AWS act as virtual firewall to you compute resources such as EC2, ELB, RDS, etc.
How Do Security Groups Work in AWS ?
-
AWS ec2 security group are attached to ENI along with many other logical components such as Public/private Ipv4 or Ipv6 address, Mac address, etc.
-
Security group in AWS uses the connection tracking mechanism to ensure connectivity establishment
Connection tracking :
-
Track the information about the traffic such as source IP address, port, or protocol initiated to the ec2 instance
-
The security group in AWS will check if any of the rules allowed for that particular Source in the inbound rule of the security group
-
If it is allowed, then the instance will establish a connection between the AWS instance and the source computer
-
There is no need for allowing the same port, and IP address protocol explicitly in the outbound rule for the traffic to leave the instance
-
Allowing all traffic in the outbound rule is enough for traffic to pass-through
-
Thus security groups are often termed stateful
Security Groups Rules in AWS
- Inbound rules
- Outbound rules
- ports and protocol
- Source and Destination
Inbound traffic : The traffic initiated to the ec2 instance from the source computer.
Outbound traffic : The traffic that leaves from the ec2 instance to the destination computer.
Inbound rules
The rules of a ec2 security group control the inbound traffic that's allowed to reach the instances
Outbound rules
The rules of a ec2 security group control the outbound traffic that's allowed to leave the instances.
Note: By default, the security groups contain outbound rules that allow all outbound traffic
Ports and Protocol
In computer Networks, Every standard protocol are having its port number. In addition to that, We can use custom protocols with custom port numbers also.
| Port Number | protocol | Standard |
|---|---|---|
| 22 | TCP | SSH |
| 3389 | TCP | RDP |
| 48000 | TCP | custom |
| 161 | UDP | custom |
| 80 | TCP | HTTP |
| 443 | TCP | HTTPS |
The maximum number of 120 rules (60 for Ipv4 and Ipv6 addresses) can be allowed in a single security group
Source and Destination
Source : Inbound rules where the source computer will be given access to ec2 instance
Destination : Outbound rules which allowed the traffic to leave destination computer from the ec2 instance .
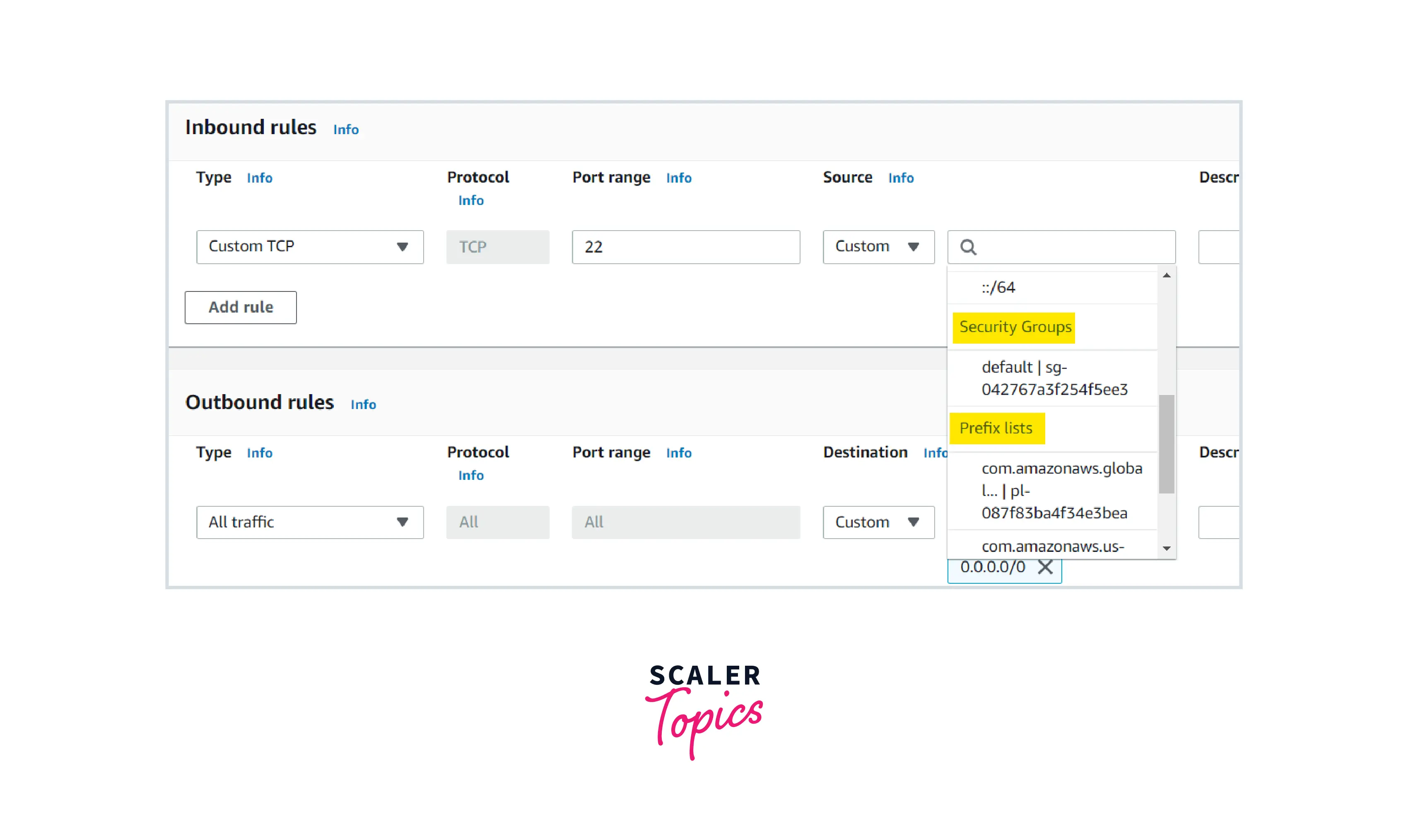
You can specify one of the following for source and destination:
- Single Ipv4 address ------------ 10.11.12.13/32
- Range of Ipv4 address --------- 10.0.1.0/24
- Single Ipv6 address -------------2001:db8:1243:1a00::123/128
- Range of Ipv6 address-----------2001:db8:1243:1a00::/64
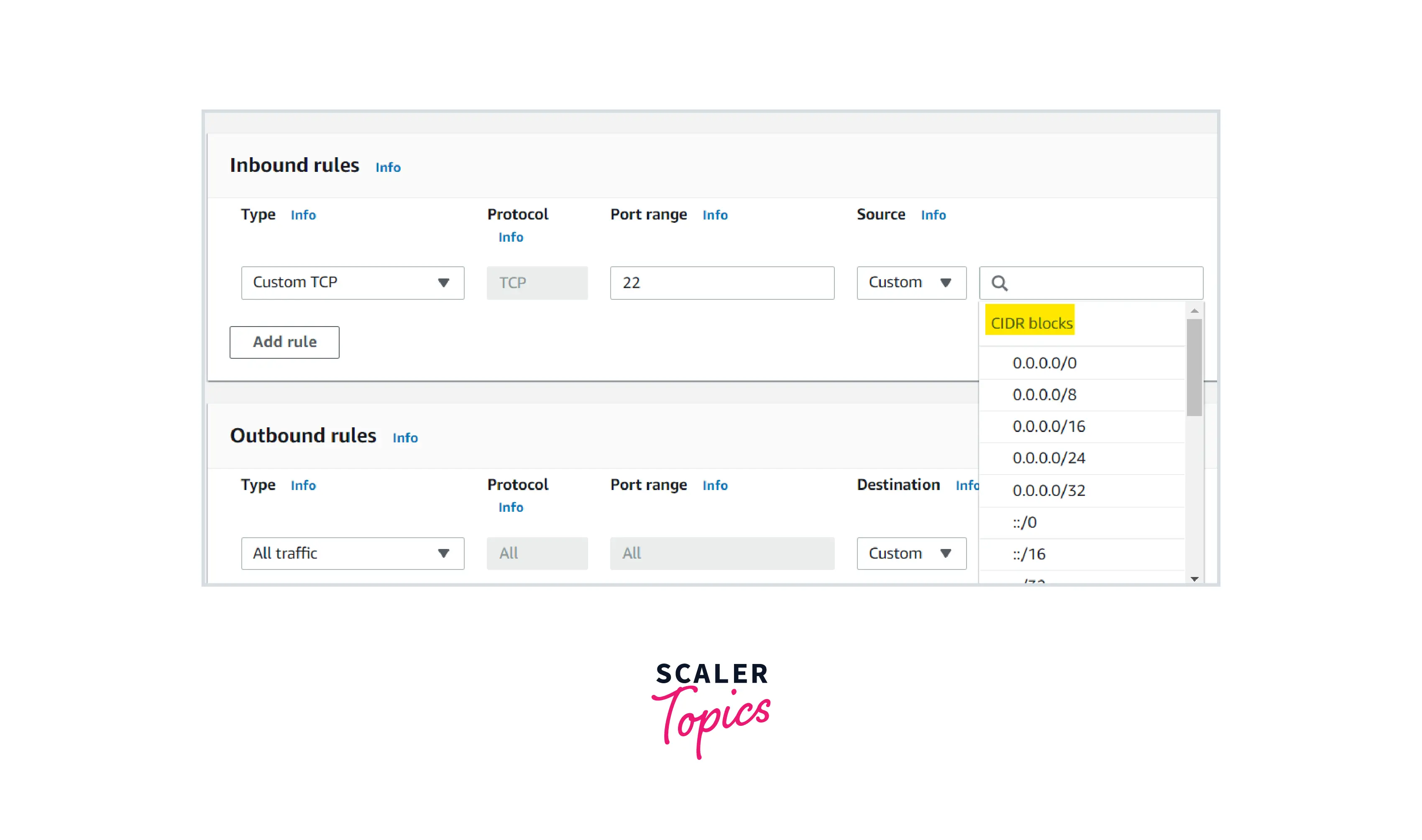
- Security group ID ---------sg-123asdfj012246
- The ID of a prefix list--AWS Managed prefix list of customer-managed prefix list
Example :
Consider if you are having one public ec2 instance running in the Mumbai region.
You would like to connect to the instance remotely.
If it is a Linux server, you can connect via SSH port 22.
Go to the ec2 instance security group inbound rule, you must allow your public IP address as a source for SSH Protocol (Port 22) to remotely connect to it.
If it is a windows server, you can connect via RDP protocol (port 3389) to remotely connect to it.
Go to the ec2 instance security group inbound rule, you must allow your public IP address as a source for RDP Port 3389 to remotely connect to it
Sames goes for web server, Database server, application server, etc.
How to Create Security Groups in AWS ?
When we launch an EC2 instance, we have two Option
- Create a custom ec2 security groups in AWS or
- If we didn't opt to create, AWS will create one ec2 security groups for us.
Custom Security Group Creation
Once you signed in to your AWS account , Search For EC2 and click it .
In the left navigation pane, you will find security group options and click them .
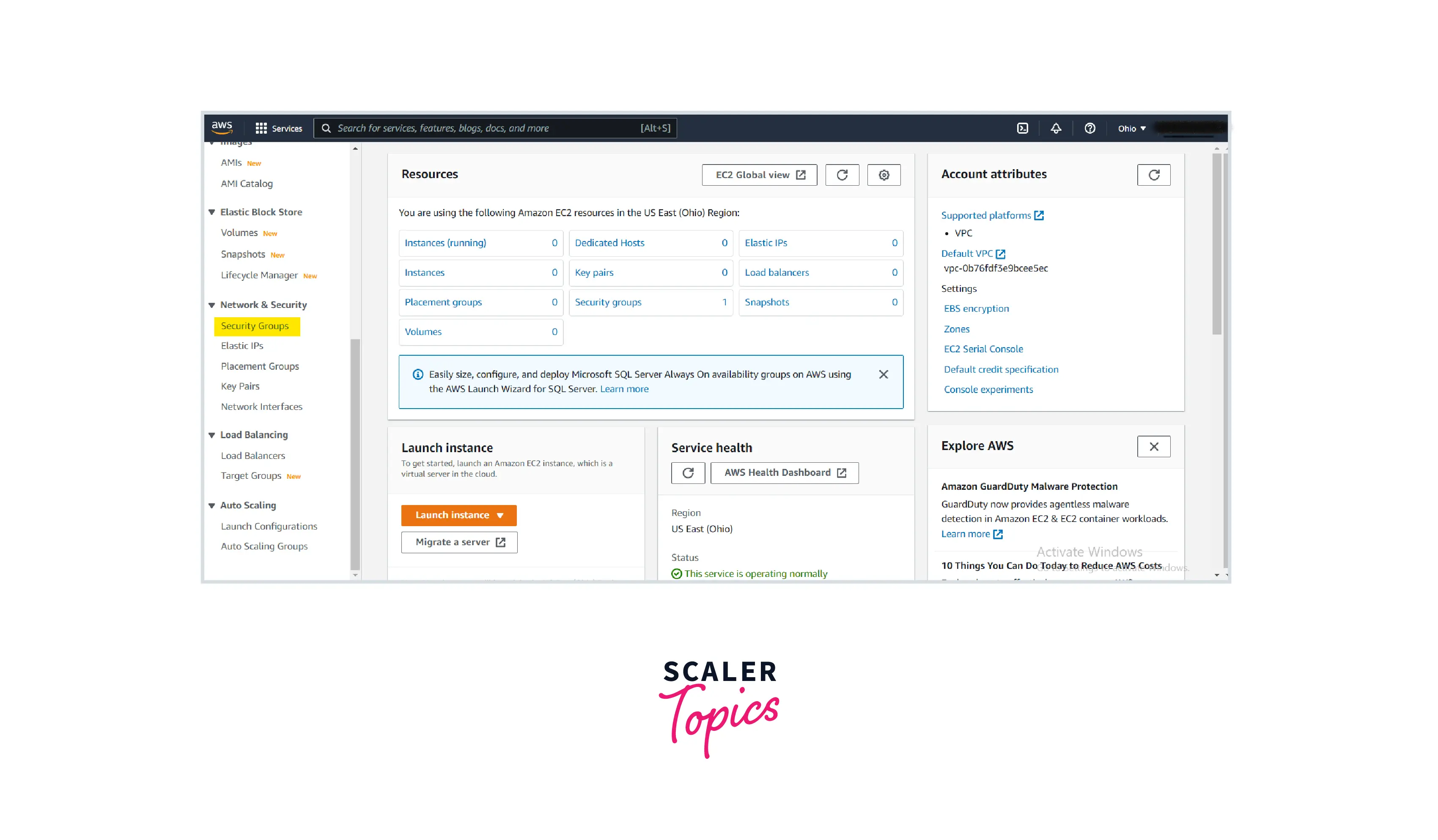
- Click Create Security group.
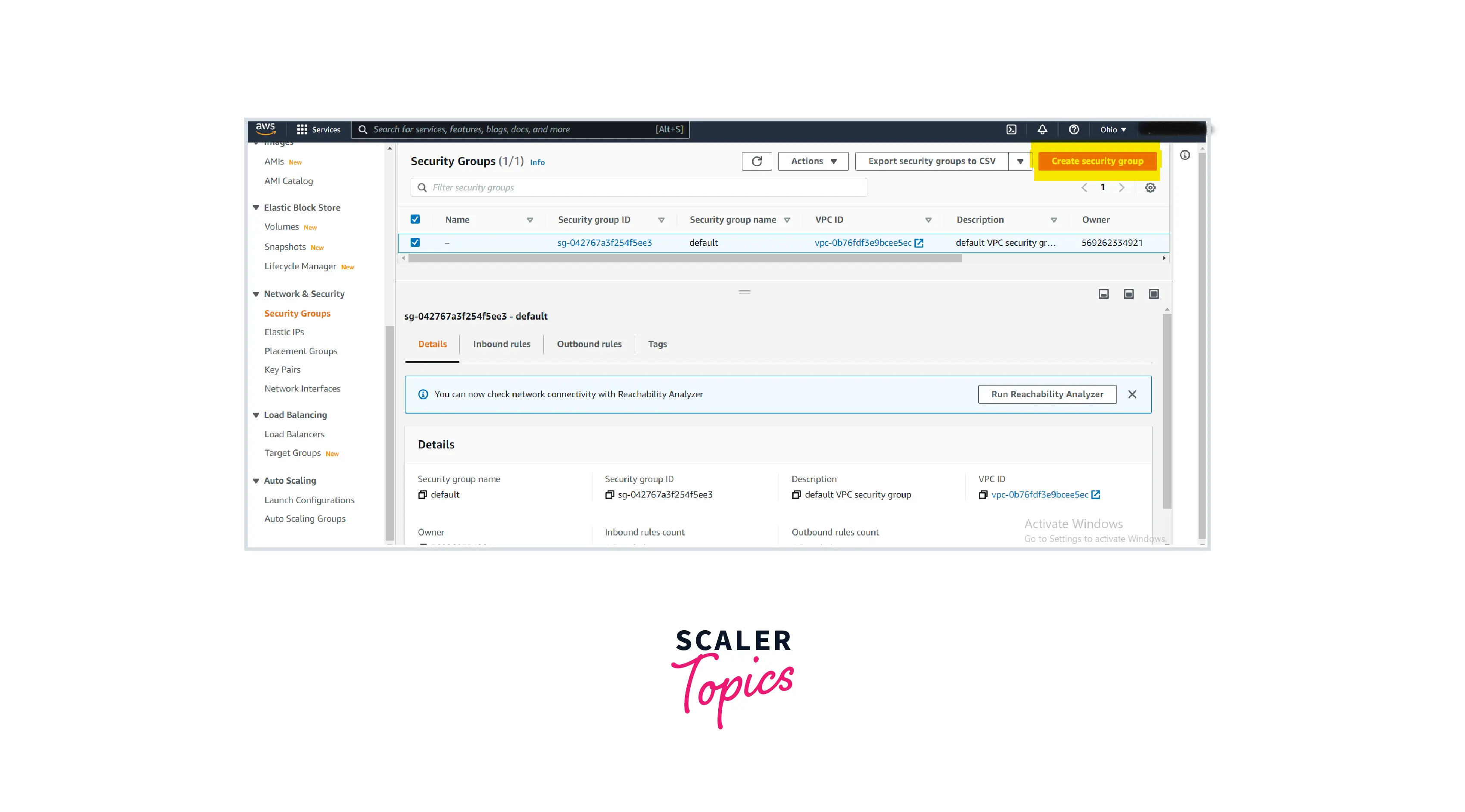
- Enter Name, Description and VPC ID
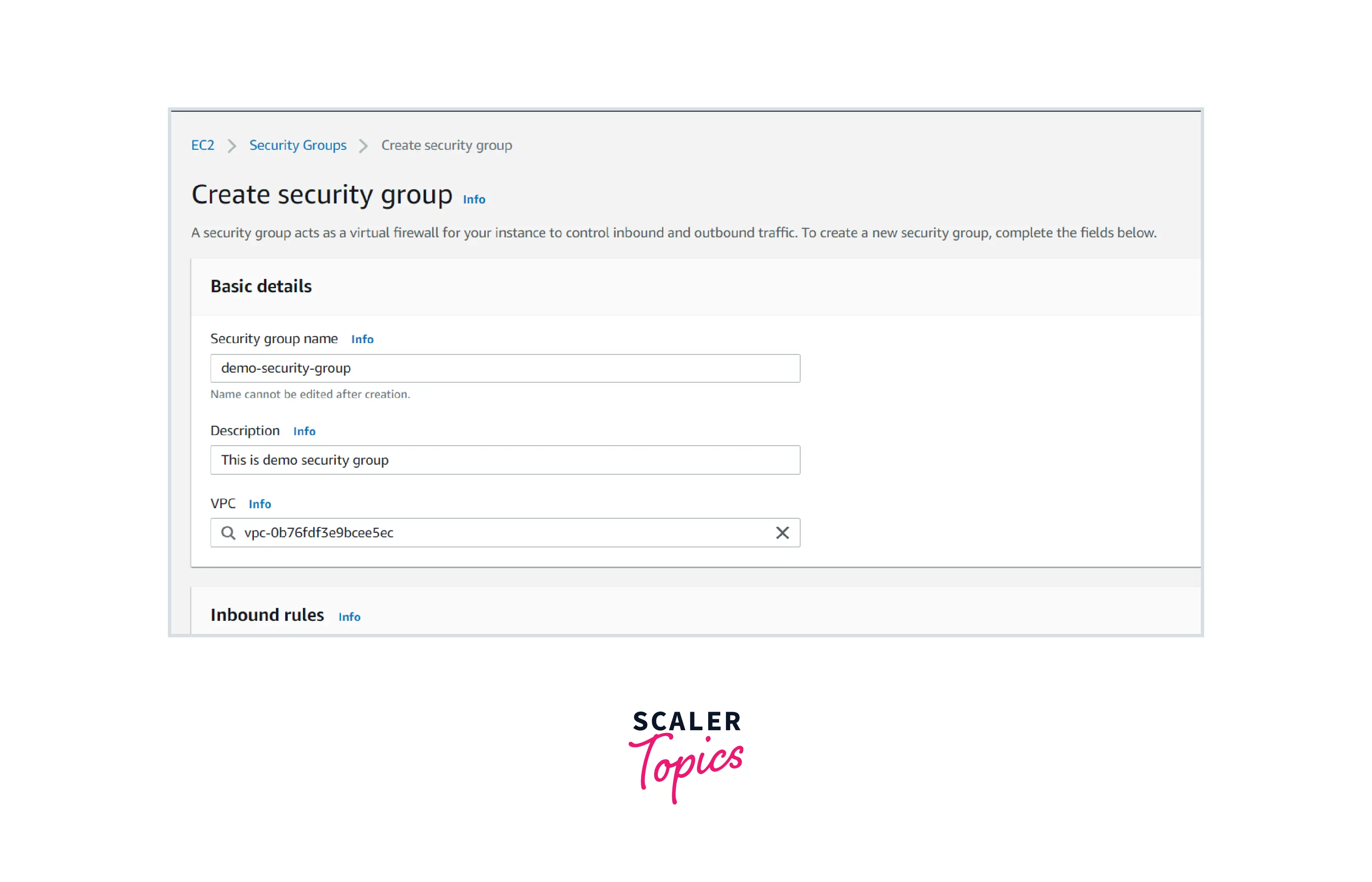
- Enter the required inbound and outbound rules .
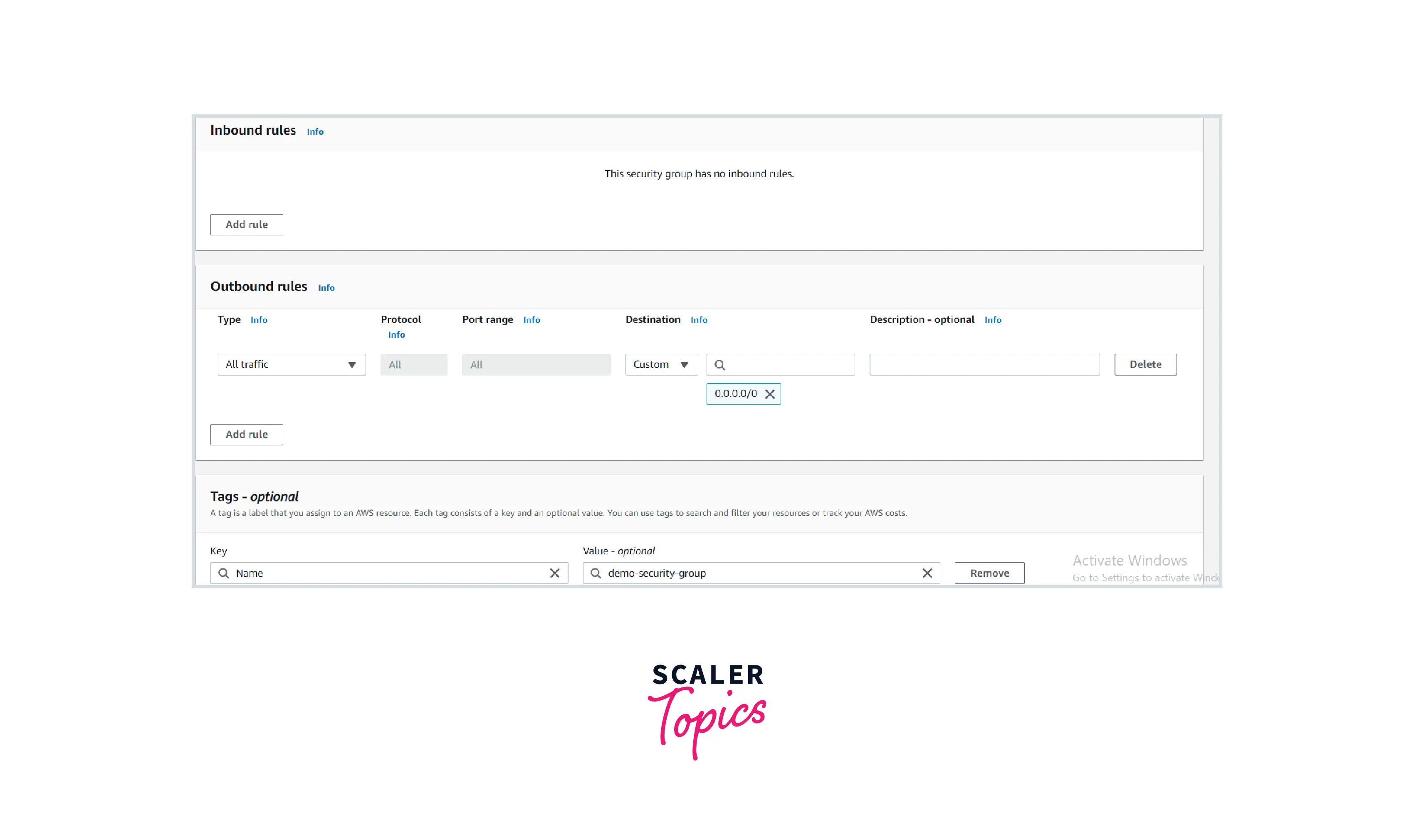
By default, there will be no inbound rules allowed and outbound rules will be all traffic allowed as you can see in this images
Best Practices for Using Security Groups in AWS
- Don’t open ports for 0.0.0.0/0 unless specifically required.
- Close unnecessary system ports.
- Categorize your security groups in AWS For eg: dev sg, test sg, prod, etc
- Enable AWS config rule for any security group changes for production environment or critical project
Using Multiple AWS Security Groups
- We can attach multiple AWS security group (maximum of 5) to single ec2 instance
- We can also attach single AWS security group to multiple ec2 instance
Depends upon the use case ,the System administrator will choose any one of the above options
Security Groups and Network ACLs
| No | Security Group | Network ACLs or NACL |
|---|---|---|
| 1 | Can be attached to EC2 instance ,RDS, Lambda etc | Associated with Subnet |
| 2 | Stateful which means any traffic allowed by the inbound rule will be automatically passthrough by the outbound rule | Stateless means that any traffics allowed by the inbound rule will not automatically reflect by the outbound rule, i.e., we should add the outbound rule explicitly to make the traffic passthrough |
| 3 | Security Group is used for instance level security | NACL are associated with an subnet and used for network level security . |
| 4 | It supports only allow rules, and by default, all the rules are denied. | It supports both allow and deny rules, and by default, all the rules are denied. |
New AWS Security Groups Functionality
- We can use AWS Firewall manager to minimize vulnerabilities and exploitation of our infrastructure by leveraging managed firewall rules .
Advantages of AWS Firewall Manager :
-
Centrally deploy protections for your VPCs.
-
Easy to generate Non-Compliance reports to take actions across our account/ infrastructure from a single AWS organization's account .
-
Easy to generate custom Audit checks for customers .
Reference : AWS firewall
Conclusion
-
Security groups in AWS are the first level of security for our ec2 instances .
-
It acts as virtual firewall to our servers / Databases .
-
We should establish AWS security group best practices to secure our infrastructure from potential exploitation/ attack .
